The danger of commercialization of Threat Intelligence
Some History
According to Wikipedia Threat Intelligence is … information about threats and threat actors that helps mitigate harmful events in cyberspace. Cyber threat intelligence sources include open source intelligence, social media intelligence, human Intelligence, technical intelligence or intelligence from the deep and dark web.
Followed by a distinction between the categories Tactical, Operational and Strategic Threat Intelligence. Whereby the following reflection is focused on the Tactical elements, which includes so called Indicators of Compromise (IoCs), such as IP addresses, file names, or hashes.
Worth reading articles on this topic can be found at SANS for example. The SANS reading room has a great white paper on identifying what threat intel is, and what it can do in best cases. Very useful in communicating with executives who might be unclear on these ideas.
And if you’ve already started a threat intel program, you can also have a look at the SANS paper on evaluating information security controls.
The danger of commercialization of Threat Intelligence
I deal with Threat Intelligence almost as long as I deal with Splunk. Threat Intelligence is an important element to put an event into context. Context in the sense of enrichment with further information. Not only to support the security analyst, but also as a preliminary stage for automated processing of events (SOAR). For the automated processing of events, Threat Intelligence feeds are indispensable.
If you think about the enrichment of information, you have already come a long way in establishing and using your SIEM.
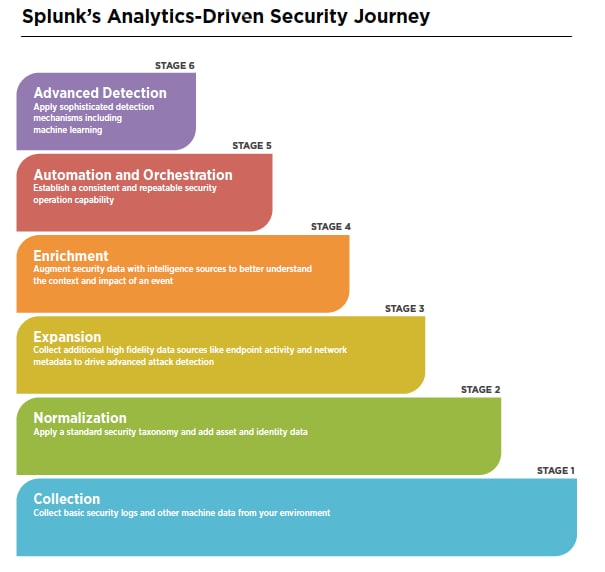
Source: https://www.splunk.com/en_us/blog/security/splunk-s-security-story-expand-your-world.html
A practical example. For the risk assessment of a phishing mail, it is useful to check to what extent the URLs used are already known. If they are known and already classified, the security analyst can check in a second step how far existing security infrastructure already detects and blocks them. If this is the case, the processing can be shortened, but if it is not yet the case, the URL can be blocked at the proxy using a blacklist. Always under the assumption that the URL list of the feed does not end up in a blacklist anyway - if you trust the external feed so far.
Give me the money
FireEye and Kaspersky are two popular examples. Both vendors of cyber security products have in the past always publicly shared Indicators of Compromise (for example in reports or blog articles). This practice was discontinued and commercial threat intelligence products were launched shortly after.
What is worrying is that the information is not necessarily based on the knowledge of vendors, but on that of customers.
The message is clear. If you want to benefit from the information, buy our service.
Pyramid of Pain
Obviously, attack indicators (IoCs) are not the ultimate wisdom. As early as 2013, the “Pyramid of Pain” was presented, which shows how much more aggravating it is for an attacker if different indicators are used for detection.
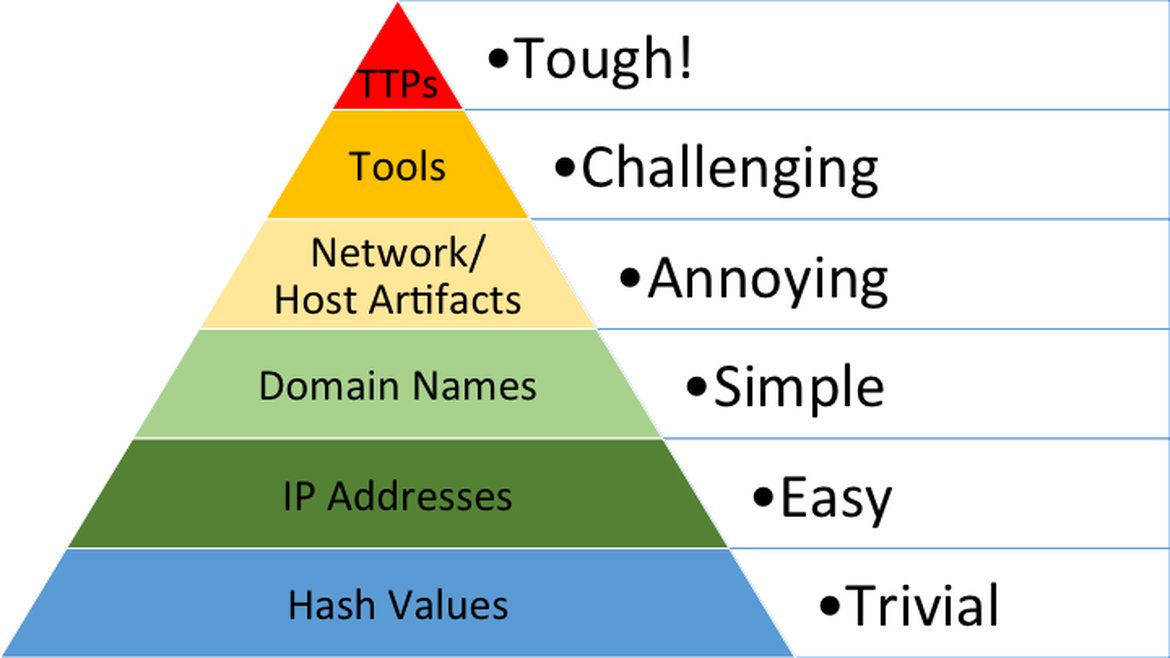
Source: https://attackiq.com/2019/06/26/emulating-attacker-activities-and-the-pyramid-of-pain/
A hash, for example, is not a nuisance, since the malware can be recompiled without much effort, and thus receives a new hash value. It is most useful to deal with the tools used (psexec, …) and the so-called TTPs (Tactics, Technics and Procedures). This means to stop the whole attack vector and not only single sympthoms.
Conclusion
There is no doubt that Threat Intelligence Feeds play an important role. Often there is also a lack of appreciation for such a free service.
However, if more and more providers of cyber security solutions decide to commercialize threat intelligence, this only plays into the hands of the attackers.
Information on Indicators of Compromise should be publicly shared, if possible. Only in this way it is feasible to react quickly and effectively to waves of attacks. Otherwise, the attackers simply test their tools on the next victim.
In an attempt to make the freely available sources more visible, I created the page www.threat-intel.xyz.